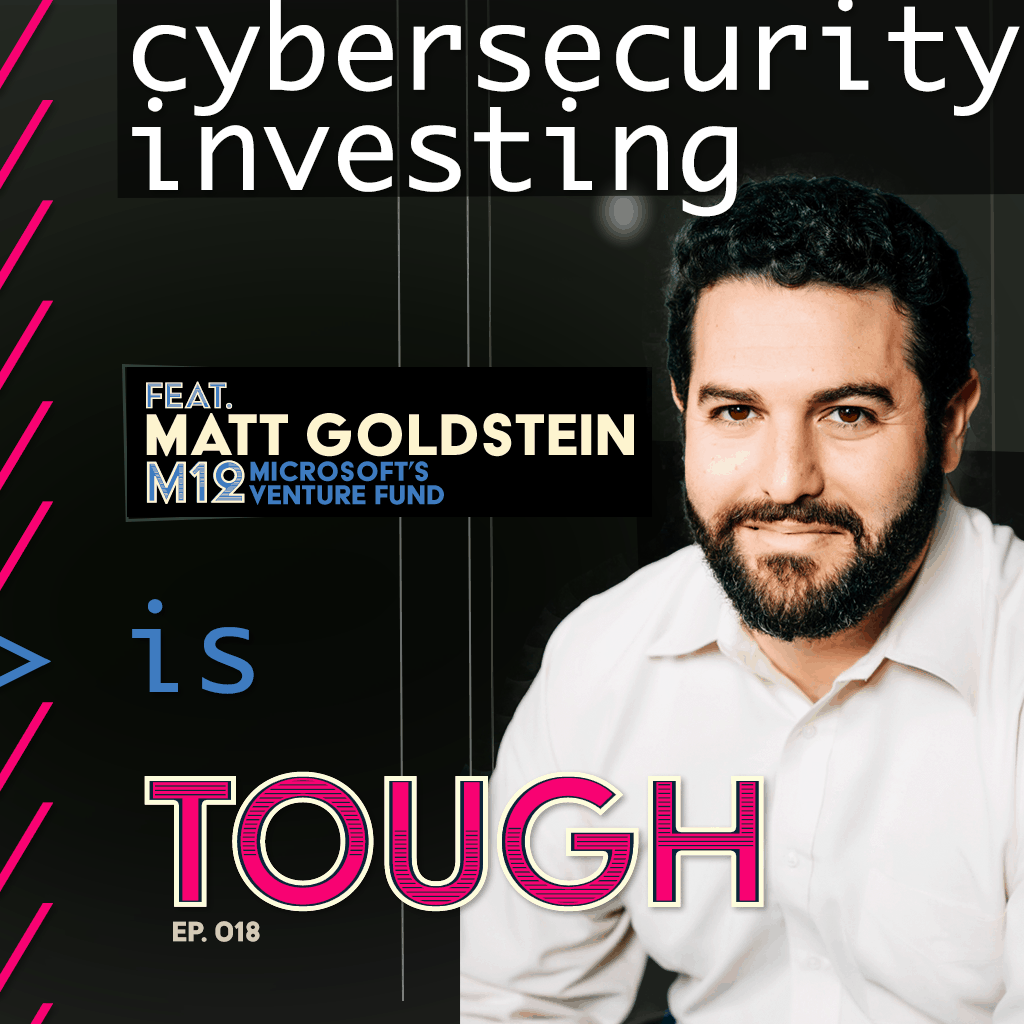
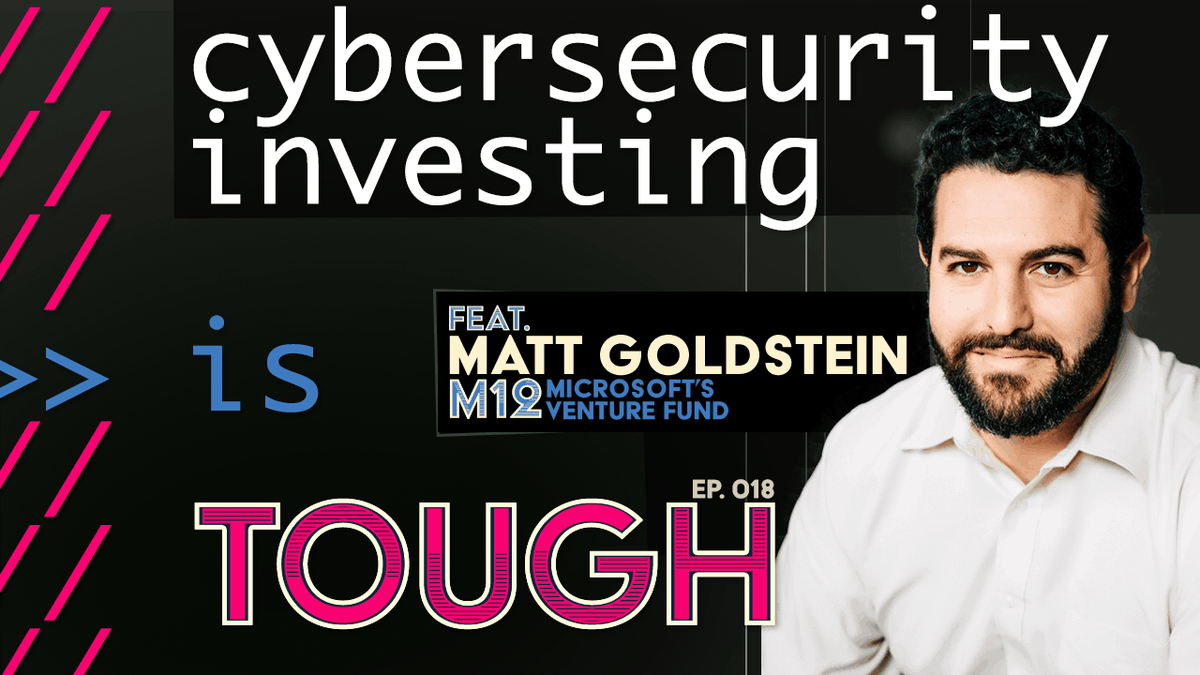
Cybersecurity investing, featuring Matt Goldstein of M12
Digitization of the physical world brings new synergies and expanding attack surfaces – so it is key to invest in those who defend us.
Probing the cybersecurity of 3D printing, scaling the digital transformation of manufacturing, and developing quantum-safe encryption for the next evolution of the Internet, Matt Goldstein, Managing Director at M12, Microsoft’s Venture Fund, shares with us the criticality of investing in companies exploring the frontiers of cybersecurity and infrastructure.
“No one thinks their front door lock is obnoxious,” shares Goldstein, yet there remains a consumer hurdle in adopting baseline cybersecurity practices such as updating software, avoiding password reuse, and leveraging multi-factor authentication. Fear-mongering is one approach, but also “it’s up to us both as cybersecurity practitioners – call them lockbuilders – as well as the homebuilders, the application builders, to make their solutions and products inherently more secure and inherently less attractive to attackers,” tells Goldstein.
Also discussed is Goldstein’s path from being a “bad software developer” to venture capital, including the workings of M12, its relationship with Microsoft, and ever-present opportunities for value creation among security startups. “Cybersecurity will never be solved. It is a fundamentally asymmetric problem. The economic incentives of attackers to get incredibly creative match the economic incentives of defenders to find newer and better creative solutions to their attacks.”
🎧 Listen:
Tune in wherever podcasts are available.
📺 Watch on Youtube:
🧠 Relevant Links:
- Episode page, transcript, and podcast listening links (this page)
- Matt Goldstein on LinkedIn
- M12 (firm): https://m12.vc
- Subscribe with your favorite podcast service
- Watch this show on Youtube
📖 Read:
- Show notes
- Live transcript and static transcript (see below)
- Topic timecodes:
- [0:00] Welcome, Matt
- [1:47] Investing in optimism
- [3:14] Importance of cybersecurity
- [5:37] Current state of cybersecurity for enterprises
- [7:45] Biggest threats
- [10:44] Digitization and privacy
- [16:09] Keeping up with frontier tech challenges
- [18:30] Selectively keeping data
- [20:13] 3D printing and cybersecurity
- [26:46] Dealing with a global marketplace
- [32:45] M12
- [36:03] Matt’s career
- [41:04] How Matt decides which investment opportunities to pursue
- [44:28] Data moats
- [49:44] Post-quantum security
- [54:39] Matt’s parting words
Matt Goldstein 00:01
Trade secrets are easy to protect when your trade secrets or the tooling and the fixtures and the machinery that are in your factory. And the only way to get into your factories to get a job there or steal the key. And by the way, there’s a guard in a gray suit walking around at night when the factory is not running. But trade secrets kind of go out the window when your business is a CAD file and all you really need to know is where’s the file, and what is the printer that prints it? Does that immediately eliminate all competitive advantage for some category of manufacturing? You better hope not.
Announcer 00:37
Welcome to Tough Tech Today with Meyen and Miller. This is the premier show featuring trailblazers, who are building technologies today to solve tomorrow’s toughest challenges.
JMill 00:50
Welcome to Tough Tech Today with Meyen and Miller. Today we have a special guest: this is Matt Goldstein, Managing Director of M12, Microsoft Venture Fund. Matt has an awesome background, we’re going to be diving into it. But to put it short, he invests in optimism, and in specific types of investments being on the levels of other frontier technologies like software services, blockchain, 3D printing, drones, the list goes on. And we will be getting into that. But first, welcome Matt.
Matt Goldstein 01:29
Thank you thrilled to be here.
JMill 01:31
So let’s go first into this investing in optimism because this is a great, interesting way to put it and I empathize completely. So could you elaborate on what you mean by that?
Matt Goldstein 01:47
Yeah, I’m a pretty, anxious, pessimistic person. And I love my job, because my job is to hang out with people smarter than me, who are solving important problems and making the world a better place. And I get to play some teeny tiny role in helping them be successful and thereby making the world better place. I would be shocked if most VCs didn’t end up in the job via sci-fi, through some way, shape or form. And, you know, my particular appetite is for the more optimistic variety. So I yeah, I get to hang out with people who are trying to change the world in ways that I find very exciting. And I’ve summarized that by… in the phrase “investing in optimism”.
JMill 02:33
So your forte I say is, one of them at least, is in cybersecurity. And for most of us on the consumer side, it means that I have to put in bigger passwords or passphrases to my phone, to my computer, to everything and then a unique password for everything. And so that can be quite a hassle and annoyance to… at least perceived to be… for a lot of folks. Could you just… to level set on the importance of cybersecurity and why there are investment opportunities in this and why it really matters to mom and dad in terms of why they should be caring about this frontier work?
Matt Goldstein 03:14
Yeah, that’s a really interesting way of asking the question. Look, the gap between the physical and digital world is shrinking every day, right? My parents have a safety deposit box that’s located at… No I’m kidding, I’m not gonna tell you where it’s located. And I don’t know what they have in it, right? Some documents or something, right? I don’t have one; I’ve got PDFs and they live somewhere. My username… No, I’m not gonna tell you that either. So this gap between physical and digital is disappearing. And, man, it’s a really interesting question. You know, humans have been building walls and building locks and devising weapons to defend themselves and their families and their property since time immemorial. So cybersecurity feels new. But it’s an obvious and natural extension to our lives becoming digitized. So it’s obnoxious, I completely agree with you that… a lot of the steps we have to take are obnoxious to me, that is — nobody thinks that their front door lock is obnoxious, right? So it’s simply a function of the fact that cybersecurity is nascent, that these tools are new, that technology is changing faster than the physical world. And it is up to us and it is up to the entrepreneurs and technologists who are building new cybersecurity solutions. And really, sorry, the people who are building digital solutions to first off make their products more secure. And second, the cybersecurity vendors to help them make their products more secure so that it can start to fade into the background. And you know, you wouldn’t think of it any more than you would think of your door lock as being obnoxious.
Forrest Meyen 05:07
So your focus is on cybersecurity and B2B companies. And have you found that B2B businesses are still kind of getting used to cybersecurity as part of the doorlock? I know that, mom and pops, like me and consumers are still really getting up to speed, but what’s the current state for enterprises?
Matt Goldstein 05:37
Yeah I mean it runs the gamut, obviously. Some industries… well, let’s see, I think you could think of it as as two different axes, right? Some industries inherently care more, and some industries inherently care less, right? And financial services inherently cares more, because they don’t want to lose money and be on the hook for it. And then the other axis might be the regulatory axis, right? Are there specific requirements, or certifications, SOC 2 for example, that they are required to achieve, I guess, would be the right word, in order to be compliant, in order to be able to offer their solution or perhaps in order to be able to offer their solution to a specific customer segment, like the government? Maybe the worst quadrant to be in is the high requirement to low inherent care, right? These are the sectors that tend to get hacked and the hacks have tremendous, far-reaching consequences for you and me: we have to reset passwords and deal with identity theft. I don’t need to point at any specific hacks in our history for us to think about the personal consequences of an enterprise being hacked.
Forrest Meyen 06:54
Sure. What industries are those that kind of meet that profile?
Matt Goldstein 07:04
I don’t have a good answer for you. I mean, I think certain arcane sub-segments of governments, the OPM hack, for example. I can never remember which credit bureau it was.
Forrest Meyen 07:19
Was it Experian?
Matt Goldstein 07:24
… yeah, they both start with E. Legacy industries that have not necessarily adapted to the digitization of every other component of our daily lives would be another classic example.
Forrest Meyen 07:44
Okay. And as far as threats go, like, what do you see is the biggest threat in cybersecurity? Like, is there a particular type of tack or hack or new technology that is really kind of the frontier of cybersecurity?
Matt Goldstein 08:03
So, I have two answers to that question. And I think both of these answers will take us in an interesting direction. One is the business model, the business model of attackers. In the past, hackers — you think about the hackers movie with Angelina Jolie way back in the day, right? It was, it was fun. It was interesting. It was curiosity. There was no business model here. That has changed dramatically. And surprise, surprise; incentives drive behavior. So to the extent that hacking is a business, and it’s an organized business, in some parts of the world, it’s a very organized business with call centers and boards of directors and balance sheets. You need not be surprised that they get very good and very professionalized. And so the challenge for cybersecurity practitioners and software developers is to… well, it’s twofold: one, make themselves a slightly less appealing target than the next guy, right? You don’t have to be the fastest person running away from the bear, you just have to not be the slowest. The other concern here is the fundamentally asymmetric nature of attacker-attackee of the cybersecurity landscape or ecosystem. Targets tend to be companies, companies have websites and LinkedIn profiles. You know who the people are. You know who their vendors are, you as an attacker can go figure out where they keep things, they have to make public filings, right? There’s a lot of information out there about any given target. As the attacker, you know, you’re not a nation state, you’re a group of individuals who may or may not be in the same building or the same city. These individuals may or may not even know each other’s real identities. So the attackers are hidden and amorphous and don’t operate on any specific timetable or schedule. They can adapt their tactics and ways that organizations can’t — operating in a public marketplace. So cybersecurity is fundamentally asymmetric. And part of my investment thesis for cybersecurity is to find ways to address that and find ways to flip that script a little bit and find ways for defensive actors to coordinate and take advantage of their shared scale, to start to flip the script and come up with a unified defense against an amorphous attacker.
JMill 10:45
With this part doing really well, in my opinion, in terms of keeping it from being the fear mongering that some folks advocates for cybersecurity have, like that the whole world is out to get my password or something, which, you know, may or may not be true. So then it seems like that there’s also this privacy angle that… you know, the rule of thumb is like if you don’t want something accessible to people, don’t put it on the internet. But as we’ve seen, through the pandemic of that we’re spending a lot of time in a place with people that we didn’t expect to be spending this much time with, or the other side, where we’re spending so much time apart from loved ones and friends, longer than we expected to. And so that latter case is where we need to be communicating through digital means. And so it’s mandatory that I’m putting it on the internet. It’s just having to ride on the internet infrastructure to do my routine communications. And so that then, I have nothing to hide argument starts to come up well, like, well, I don’t need an encryption, because I’m just talking about my cat. But what’s more at the heart of that privacy need?
Matt Goldstein 12:03
Yeah, look, I have family members who work in a in-person job, do not participate in social media, do not have any IP messaging, right? They have a mobile phone that they use for phone calls, and the occasional text message. Their job does not require them to log into anything on a regular basis. And cybersecurity is still relevant to them, right? Both to your point about privacy and the simple fact that you don’t need to to participate in an ecosystem to be a record in their database somewhere. And thinking more about the business models of attackers: identity theft, trading corporate corpi, a PII of personal data. You don’t need to be an active participant in this ecosystem to be threatened by it, right? So the concerns apply to everybody. But to your point about about fearmongering. You know there’s an element of education, certainly. I don’t think you need the cops pounding on your door and saying, did you remember to lock your door to just learn as you grew up, that you generally lock the door when you leave the house. At the same time, as I said at the beginning, it’s up to us, both as cybersecurity practitioners, call them lock builders, as well as the home builders, the application builders, to make their solutions, to make their products inherently more secure and inherently less attractive to attackers. For the last 20 years, the business models of, not attackers, but of the internet, have focused on collecting more and more data. And we’re starting to reach a point where maybe collecting all that data is a liability. And maybe keeping that data as a liability. And maybe a better business model is to purge data and not have anything, not put your crown jewels in the kitchen window that face the street, right? Because you just don’t have them. Because you’re a little bit more of a minimalist. So I think there are economic considerations, business model considerations for both attackers and attackees, attackers and technologists and software developers that need to be considered before we even start getting into this whole shift left, build a more secure application, build a more secure house, and then the next layer of the onion which is what cybersecurity vendors do I hire, what solutions do I purchase, how do I configure them, how is my cybersecurity team trained, how do I train my employees to be vigilant? These are layers of the onion that are critical, but that could be so much thinner if we just did a better job at the beginning.
JMill 14:53
If I’m, say, medium sized business or a corporate intranet, and I thought I would have been doing right by adopting solar winds and the list goes on in terms of tools that seems like everybody’s vetted it, seems like it’s going well, and in many cases, folks have vetted it. But there’s these the zero day attacks and other forums that make it so that the world shifts really quickly. Is there a sort of, based on your sort of view as an investor in the next generations of these kinds of security measures and technologies, is there advice to the admin, the person who is… he or she has to work with commercial off the shelf technologies, but they’re being faced with sometimes frontier tech kind of challenges…?
Matt Goldstein 16:09
A microscopic percentage of big breaches are the result of incredible technology innovation on the part of the attackers: a microscopic percentage. Keep your software updated, configure it correctly, and enforce good cyber hygiene, password hygiene and other related topics and you have eliminated 99% of the attack surface. But okay, people are still going to buy cybersecurity solutions. So there’s this concept that’s been around for a long time called defense in depth, which any real cybersecurity practitioners who are watching this are gonna laugh for my poor explanation of it, but look, it is the layers of the onion, it is wrapping layers upon layers of application security and web application firewalls and authentication services, and identity services; it’s just wrapping things over and over and over again, so that if something gets breached, you have another layer of security underneath it. But the problem here, as evidenced by the SolarWinds attack, is that every one of these things that you wrap is in and of itself, an attack surface. Software is not perfect, unless you’re NASA and doing kind of formal verification.
Forrest Meyen 17:37
Even then it’s not perfect.
Matt Goldstein 17:38
Yeah, I know. I thought that was… generally speaking, software isn’t perfect. And so again, you’re much, much better off not getting too creative, exercise really good hygiene, keeping your software updated. And then, you know, very slowly and deliberately identifying the specific elements of your business, not just your infrastructure, but your business that make you vulnerable, identifying the assets that people are interested in, right? Is it customer data? Is it employee data? Is it payment information? Is it.. I don’t know, what else? Those are some examples. Can I retain less of that? Can I get rid of some of it, so that there’s less to be exfiltrated?
JMill 18:30
So it sounds like it’s a bit of a case where we’ve been sort of high on the hog, so to say, of, of ingesting more and more data, and everybody wants to have their own sort of fiefdom of data so we can do big data things on it. But really, now it’s about… let’s be really selective about what we truly need to know and to work with.
Matt Goldstein 18:50
That’s exactly right. And then taking it a step further, this whole concept of zero trust, right? It’s all about conditional access. So maybe we keep something because we need it, but under what circumstances do we need it? What are the processes and procedures tfor getting access to it? You know being very careful and selective about the data that you keep, where you keep it, when you keep it. I mean, again, these aren’t even cybersecurity topics; these are just like life, right? These are just kind of personal hygiene topics.
Forrest Meyen 19:22
We kicked off this discussion talking about how a lot of the physical world is now being digitized. And another interesting, you know, set of investments in your portfolio is 3D printed. So I see you’re an investor in Markforged, which is a 3D printing company, not too far from me, actually. So that’s the digital world becoming physical. I wonder if you can talk a little bit about what makes 3D printing really interesting, and how do you think it’s gonna be used in the future of business, like in the next 10 years.
Matt Goldstein 20:04
Yeah. Do you want to talk about the cybersecurity of 3D printing?
Forrest Meyen 20:07
Well actually, yeah, that’s a good transition. I’m curious. Yeah, yeah, go ahead.
Matt Goldstein 20:15
So I’ve known the Markforged team since 2014 or 2015. David and Greg are two of the smartest people on the planet, as far as I’m concerned or aware. I am not a mechanical engineer. It’s not space that I knew well, and certainly not a space that I continue to know well enough to claim being an expert by any stretch the imagination. So my initial investment was really just a bet on the team and on the market. And on this fundamental belief that supply chains would need to get shortened, that just-in-time manufacturing means just in time for every component. And that 3D printing in its various forms was inevitable. I prepared some talking points on my favorite books, because, as I said at the beginning, I think everybody comes into this industry via sci-fi in some way, shape or form. So it was Neal Stephenson, however you say his name. He’s my boy. So Cryptonomicon is the thing that kind of created my interest in cybersecurity, certainly, but startups and venture capital more broadly. He had a follow-on-work Diamond Age, which, which is the thing that taught me a lot about 3D printing, but it exposed me to the fantasy of what could be possible in the not too distant future. So yeah, invested in Markforged. And been with them on the ride of our lives for the last six years. And of course, they’re in the process of SPACing, which is pretty cool. And then I have another cybersecurity investment company out of Israel called Nanofabrica, which is doing nanoscale 3D printing using a twist on a Vat Polymerization technique. So teeny tiny parts that need to be incredibly accurate. Look, for both Markforged and Nanofabrica, whether you’re talking about a shift lever on a motorcycle, like the one that Markforged has always had in the front of their office, or you’re talking about something that’s part of a medical device, or a component that’s going to get embedded somewhere in your body or threaded up a vein or an artery somewhere. You know, historically, the process for manufacturing these things was… I think the Markforged deck used to have this picture of this guy working a CNC machine, and he was in his 70s, wearing the blue overalls, and they always called him Frank, right? The answer was always Frank, right? You’ve got this custom part, and you send it off, and that person sends it off, and that person sends it off. And at the end of this chain of sending off these designs, and these parts was Frank in workshop operating the CNC machine. And we think about scale in every component of the technology industry, it’s always about scaling the work that we do, and you can’t scale manufacturing if you can’t digitize the process. So an overarching theme of all of our investment activities is digital transformation, and why shouldn’t manufacturing be digitally transformed? And digital transformation manufacturing doesn’t just mean cooler Kanban boards or touch screens on the line? Like why can’t some of these actual actions be taken by machines? And why can’t these machines be kind of operating in a recurring fashion? Just just like a just like a lambda function, right? Or just like a microservice somewhere? Why can’t manufacturing be a microservice’s architecture? So that’s what inspired my interest in the space; beyond that, it’s been very kind of team driven, looking for new technologies and the teams that are capable of executing on them, trying to ignore the 3D printing market size — I think that’s the most common objection we hear to investments and say, look, this is not about 3D printing, this is about manufacturing and what is the market market size of manufacturing? Well, it’s everything right? Everything that isn’t software is manufacturing in some way, shape or form. So looking at the CNC market, looking at the EDI market… looking at the EDM market, excuse me. 3D printing will grow the pie, right? All of these are grow-the-pie technologies. Cybersecurity for 3D printing is a cool topic. I get yelled at whenever I use this term, but DRM for designs, right? DRM for CAD models. Everybody hates the word DRM and so they get all touchy when I when I use the phrase. When I lhear the pitch, I’m like, oh, god, so you’re building a DRM for CAD models.
JMill 24:55
For the audience, in case you haven’t been…
Matt Goldstein 24:59
Yeah, Digital Rights Management. We’re all old enough that we dealt with ripping DVDs and ripping CDs.
Forrest Meyen 25:07
Back when Napster was cool and no one knew it was wrong.
Matt Goldstein 25:12
Not that any of us have ever have ever ripped any content from any source ever. But trade secrets are easy to protect, when your trade secrets are the tooling and the fixtures and the machinery that are in your factory. And the only way to get into your factories to get a job there or steal the key. And by the way, there’s a guard in a gray suit walking around at night when the factory is not running. But trade secrets kind of go out the window when when your business is a CAD file, and all you really need to know is where’s the file and what is the printer that prints it. Does that does that immediately eliminate all competitive advantage for some category manufacturing, you better hope not. National security concerns, right? A lot of these 3d printing companies have big military and defense customers and contracts. Because the things that they’re making go into other things that we’re not supposed to know about. And I don’t know about and that’s fine. I don’t want to know. So how do you protect this stuff? It’s not just a matter of protecting the file, but understanding when it’s used and how it’s used,. instrumenting files that can communicate with a central service. Back to back to my earlier point about what do you keep: should we be keeping all the previous versions? Where do we keep it? Who has access to it? What can you do with it? As I said at the beginning, the separation between physical and digital is shrinking in both directions, and so cybersecurity applies even to the 3D printing market.
JMill 26:47
The intersection of the physical and the digital is really an interesting point and about the sort of… is my whole business just a CAD file? And extrapolating that out to the global… nation state level, you’re based and invest from the United Kingdom, do work with a lot of sort of companies spanning the globe and a company Microsoft, ultimately that’s global… what kind of differences and whether it’s toward nationalism, sovereignty, etc., what kind of differences are you seeing in the market and the mentality of the folks that you’re working with?
Matt Goldstein 27:34
Yeah, interesting question. So as you point out, Microsoft’s a global company, and when we started M12 about five years ago, Satya said to us, Microsoft’s a global company, we want you to be a global firm. So it took a while. You can’t kind of flip a switch and go from a three person team to a 10 person team, spread around the globe and trust each other and understand each other and be able to do deals together. But we have scaled up over time. So we now have five or six investors in San Francisco. I moved to the UK about 18 months ago to to open up our European presence. I’ve got three colleagues in Israel and Tel Aviv and one in Bangalore in India. I mean, it’s an entirely separate topic that we can spend as much time as you want on but this general concept of kind of pre versus post-COVID: startup location, companies are global, companies are remote, the Silicon Valley diaspora has really accelerated. Oh, and by the way, as long as we’re close enough on timezones, I don’t really care where you sit at all, kind of lowering the bar to taking a meeting. And hopefully that means that we’re all a little bit more inclusive in our investing activity and investing practices. Yeah, it’s a cool topic. In the domains where I spend time, I mean, B2B broadly, but cybersecurity and infrastructure. Let’s see. So there’s this macrotrend of trying to keep… quote unquote, keep China off the cap table. It just represents risk to entrepreneurs and to founders, in terms of where you’re able to raise follow-on capital, who’s willing to be your customer, you’re probably not going to land a US or a Five Eyes revenue contract. If you have too much… quote unquote, too much China on your cap table, it can become a concern for investment rounds, it can become a concern for exits. I am by no stretch of the imagination and expert on CFIUS. Nor can anybody who’s not an attorney get to a level of sophistication and comfort on CFIUS. And so we just simplify, we really have no choice and we simplify by just trying to keep China off the cap table.
JMill 29:56
Could you elaborate a bit on… in terms of why that is… of the keep China off the cap table? It’s not just like a particular country that they want to just like, as a newcomer entrance or something… there are more sort of nation state reasons for trying to avoid that kind of investment, right? And some sort of historical precedents for being concerned about…
Matt Goldstein 30:24
I mean, look when you’re tiny, you think geopolitics means nothing to you. When you’re larger, geopolitics are surprisingly relevant to the day-to-day job of a founder and a VC. Because you’ve got to exit somewhere and sometime: somebody has to buy you or you have to go public. And in the meantime, you have to close a bunch of revenue. And in the meantime, you might be taking out debt or hiring employees. And as you go through all these processes, people want to understand who owns you, who’s on the cap table, who are the beneficiary owners of the work that you’re doing, who has control over the business, who has board seats. Washington is not incredibly nuanced, right? They sometimes they don’t take for granted when we say, oh, they own 10%, but they don’t have board seats, they don’t have information, so it’s just passive. That’s not satisfactory. That’s not a satisfactory answer. So sometimes we have to be very careful because what a shame that you’re going out and trying to close a big contract. And the company is unwilling to do business with you based on a million dollar investment you took five years ago from one particular party. So you have to be unbelievably careful. That is doubly a concern when you’re talking about sensitive IP, certainly within the cybersecurity realm, or really anything inside of the cybersecurity world, but going a layer deeper, anything that deals in cryptography is incredibly sensitive; export restrictions: ITAR, right? Again Washington is not always willing to accept, oh, they’re just a passive investor. Well, okay, do they get to come to your board meetings? Have you ever afforded them a demo copy of your software? Did you breach ITAR restrictions by forwarding them a copy of your demo that happens to use some cybersecurity somewhere in it? Did they get a demo of the product in order to make the investment? Did you breach ITAR, then? It’s terrifying. The tiniest misstep can can really screw up your business. So unfortunate as it may be, and I say this as somebody who lived in China for a couple years and studied the language, in many cases, you just have to keep China off the cap table.
Forrest Meyen 32:44
So can you talk a little bit about just M12 as a whole, what your strategy is, what kind of makes you different from a traditional VC.
Matt Goldstein 32:58
Sure. Yeah, M12, we’re 5 years old. We launched in 2016. Anybody who spent too much time in the valley has heard and probably has rightfully heard to be kind of careful or cautious around corporate investors, corporate venture capital; the argument has always been, their incentives differ from institutional investors, and from those of the entrepreneur. People come and go, strategies change, the groups get stood up and shut down. And the short answer is, I agree with all of that, and it’s largely true. All that said, I’ve always believed that corporate venture done right, should be better, not worse than institutional, because we have more to offer to entrepreneurs than just my charming personality in your boardroom. Or if you’re Andreessen, the 100 people that they have on their platform team. So, we drew a lot of lessons from our friends at Google Ventures, GV, as they prefer to be known. The point being, you can build a professional, institutional grade, financially driven venture firm, that also happens to have access to the corporate parent, and use that access to drive value, unique differentiated value that no other investor can drive for the portfolio companies. And as a result, make everybody happier: you’re driving specific value for the entrepreneurs, you’re making the rest of the cap table happy. Your corporate parent is engaging with startups and meeting them earlier than they would otherwise. And hopefully, everybody’s making a bunch of money in the process. So that’s how we’re structured. That’s how we operate. We’re about 30 people, 10ish on the investment team. We have two platform teams, market development and portfolio development. Portfolio development is all about opening doors to Microsoft: they’re not quota-carrying, they’re not here to shove anything Microsoft down anybody throat, they’re here to count on doors, grease the skids and try to help our portfolio companies create the relationships that they’re looking for with arguably the largest, most important B2B software company in the world. Market development focuses on helping our portfolio companies engage directly with potential end customers, often those are Microsoft customers too but trying to go directly to the Fortune 500 or or the Fortune 450 (term I invented, the fortune 500 minus all the other software companies). Yeah, trying to help our portfolio companies land revenue from some of these other large enterprises. So that’s what we do. We are we are early stage B2B investor, we’re focused on series A and B, we invest in anything B2B, where software is the point of leverage, and then we have this incredibly unique differentiated value at which is unparalleled access to Microsoft.
JMill 36:03
So let’s talk a little bit on the personal side that has led you to this really interesting position… so I think a lot of folkswould be curious as to how did younger Matt get into this opportunity to be able to look across the across the world for some awesome frontier tech?
Matt Goldstein 36:25
Yeah, so I started my career as my resume quite literally said for quite a while a bad software developer, you know self taught. Yeah, I just I want to make sure nobody quizzes me, right? So I was self taught and worked for systems integrator doing CRM systems integration work first job out of college, or out of uni, as I’ve learned to say here, and then slowly worked my way into the startup world, spent several years as the very early employee with a venture backed startup in the automotive space. So this was the the mid 2000s, there were four or five automotive startups that raised hundreds of millions of dollars to build new cars and bring them to market. You’ve heard of one of them, that would be Tesla. I did not join that one. I joined one of the other ones. We were trying to build the cheapest car that an American would buy 4-doors, power windows and locks, air conditioning, CD player, automatic transmission, brand new for $10,000. Incredibly cool company, incredibly cool story and ambition, raised about $110 million in venture capital, lost all of it. That’s a story for another time. But suffice it to say, losing $110 million is a great story to tell when you’re trying to get into business school. So that’s what I did. And starting my MBA, not knowing the difference between a mutual fund and a hedge fund, not being a finance guy by any stretch of the imagination. love startups, I love tech, I had no idea what I was gonna do. Found myself in a conversation with a San Francisco based seed fund. Charmed them through my arcane knowledge of B2B software and SAS before SAS was really a word. I think these days if you were to go into any of these MBA campuses, the number of people who came from enterprise software came from B2B software is a much larger proportion of the class. Back then I was unique and exotic. Landed an internship and within about two weeks decided, this is exactly what I want to do. If you’re geeky, intellectually curious and have just a little bit ADD, I can’t imagine a more fun job, right? My job is to get coffee with people smarter than me and ask them questions. And you slowly start to figure out your style and your focus areas and the things that you have an interest in and hopefully a little bit of domain expertise. And if you don’t have the domain expertise, you can build it over time by just meeting hundreds and hundreds, if not 1000s of companies in a particular domain. And that’s kind of how I ended up in the industry. Cybersecurity specifically, I joined a firm called Trinity in 2012. And on my first day or second day, one of the partners said, go sit next to that other guy and go build a cyber practice. Because I think they had a sense that this was an important sector. And it wasn’t a sector that they’d spent an enormous amount of time in the past. And how many years is it later? What was that? So about eight years later. I’ve made half a dozen cybersecurity investments. I’ve met well over 1000 cybersecurity companies. I aggressively stopped short of calling myself an expert, but I think I know enough to be dangerous. And I know the landscape. And cyber as a investment sector is the gift that keeps on giving. It’s the industry that never goes out of fashion, the problems are never going away, and cybersecurity will never be solved. And you could view that as a cynical statement, right? Like, I don’t want it to be solved, so I can keep making money. That’s not what I’m saying. I’m saying it is fundamentally asymmetric problem. And as long as that asymmetry exists, the economic incentives of attackers to get incredibly creative match the economic incentives of defenders to find newer and better creative solutions to their attacks.
JMill 40:46
What am I gonna do with my bit… my crypto wallets, then? How am I gonna keep those safe?
Matt Goldstein 40:51
I don’t… I have done one crypto investment. It’s not a space that I feel super comfortable talking about.
Forrest Meyen 41:04
So when you’re meeting these companies, I mean, you talked about Markforged, you already had kind of a relationship with the founders and knew them very well. But when you have that first meeting with founders, what’s kind of like the indicator to you that that you’re interested in a follow up meeting? Do you get a gut feeling? Is it just great people? What really makes the decision whether you want to go further?
Matt Goldstein 41:33
I have two answers to that question. One is… so one of the biggest things that I’ve learned through the COVID era has been that we can do our job entirely remotely. I’ve made two investments now without ever meeting the teams in person. And while I do think it’s important to eventually meet them, and I look forward to going to board meetings again someday soon, and building a more personal relationship with these executive teams, we were able to do it. And part of what we did was we did, we did a lot more diligence. And I think our decisions were more thesis driven and more data driven, and less gut and heuristic driven. And I am not saying that gut and heuristics aren’t important: you know, venture capital is the art of making decisions in the absence of perfect information. So gut will always play a role. But I think that the days of in person first meetings with entrepreneurs are over. I think it’s healthier for me, I think it’s healthier for the ecosystem, I think it will hopefully lead to more diverse and inclusive investing. So now my approach is meet everybody remotely at the beginning. Do as much diligence as I can up front. And then again, I look forward to eventually meeting people in person again, one day and using my gut and using my heuristics to verify my diligence and not the other way around. To the broader question and how it relates to cybersecurity, certainly being thesis driven. On the one hand, knowing what you’re looking for, on the other hand, I always say, it would be a disaster if I knew more than an entrepreneur about the sector that he or she is operating. That’s not how it should be, right? I’m a generalist. And there are things that I know a lot about like fundraising, and VC fund operations, but the specific nuances of my portfolio companies, businesses is not and should not be one of those spaces. So within cybersecurity, there are certainly things that I look for. I look for data moats, and that’s, I think, a topic we should spend another minute or two on. But taking a step back from there, cyber is a unique and distinctive technical domain, and you see almost no movement back and forth between kind of traditional software developers and cybersecurity developers. (I was trying to think of a good metaphor for that, I don’t have one right now.) But so the short answer is, in cyber, I look for a lot of domain expertise, and experience in addition to the other more general things we look for in any investments, in addition to hopefully something that checks a particular thesis box that I’ve been working on or developing.
Forrest Meyen 44:28
Great. And you said you wanted to touch on data moats. I think now would be a good time, what is the data moat? I’ve never heard that.
Matt Goldstein 44:35
So maybe I over prepared. Because I was just nervous that a bunch of experts were gonna make fun of me after after you post this. So we were talking about asymmetry. And I was saying, my philosophy and my approach to making unique and differentiated investments in cybersecurity is to try to do things that start to flip that asymmetric equation, that start to allow for alignment and shared scale between large, stationary enterprises that can’t disguise their borders or their perimeter or they can’t disguise their assets. They are what they are. But we have other advantages, and our advantages are scale and our advantages are that we’re on the right side of the law. And our advantages are or should be that we can coordinate with one another. In the past, that’s been very difficult: it’s been very difficult because of data management and privacy and data access. So tools and techniques, whether they’re graph databases, or federated learning, are starting to enable types of coordination that couldn’t exist in the past. And when that coordination is applied to cyberdefense, I think it becomes very powerful. We have two investments in our portfolio cybersecurity investments that I describe as a giant graph database upon which they build some cool products. So one of those is SpyCloud. And I wanted to make sure I use their language, not mine. So SpyCloud gives you access to the world’s most comprehensive repository of compromised credentials and PII. So on the one hand, they’re probably the most attractive asset for attackers in the universe, because they have… I don’t know, billions, right? Where are the notes? … 118 billion recovered breach assets, 23 billion total passwords, right. So when they…
JMill 46:38
That’s quite a nice pot to go after. That’s like bigger than one basket or something…
Matt Goldstein 46:44
Yeah, when they… I assume I can tell the story… when they came in and gave a demo to Satya, they liked paused and was like, so can we do the demo? And Satya, can we can we use you? And he said yes. And kind of went into Maltego and the graph database and pivoted from asset to… you know, here’s this name, so here’s where we think his email addresses are, here’s where we think his phone numbers, is this your password? Oh, dang. Right? Now, obviously, once you get this enormous corpus of data, what do you do with it: you build products, and the easiest to explain product is password reuse prevention, assume they have a better term for it, but essentially safeguarding the identity of employees and users; you go to reset your password, or you’re asked to reset your password. It’s got to be this long, it’s got to be this complex. And it can’t be a password you’ve used here before. Oh and by the way, it can’t be a password that you or anybody else has used anywhere ever in the history of the internet. That’s pretty cool. That’s pretty cool. So that’s one product you can build on this data moat. And it’s the kind of thing that you can only achieve with scale and with coordination. I promise you metaphors, I do love metaphors. The other company that operates in a very similar similar vein or similar domain is called HYAS, H-Y-A-S, HYAS InfoSec. They’re entirely focused on adversary infrastructure, right? So the command and control infrastructure, the servers, the domains, the IP addresses that attackers use for coordinating their attacks for operating their botnets. So here’s my favorite metaphor. I love this one. Think of an organization as a prison, and think of the cybersecurity team, as the guards and they’ve got x-rays, and they’ve got pat downs, and they’ve got bars on the windows and they scan all the produce that comes into the kitchen area. And the warden is absolutely sure no cell phones have been snuck into my prison. We are an illicit cell phone free zone, we have the best security, no way anybody snuck a cell phone in my prison. That’s cool, but I’m just gonna go check the cell tower across the street from the prison, and I can see 11 SIM cards pinging off of it. I don’t know how they got there. I don’t know who snuck them in. But they’re unaccounted for. And they’re pinging off this tower, which means they got it. So by instrumenting the infrastructure, going directly to the cellphone towers, to the infrastructure of the global Internet, dumping a bunch of stuff into a giant graph database and then building products on top of it, you could start to flip the script. And this is another example of coordination and building these data assets that create defensive tools and products that couldn’t have existed in the past, and I find those really exciting so that’s the kind of thing I’m looking for.
JMill 49:44
So the history of security, and let’s keep it specific in terms of like cybersecurity, is you got the white hats, who are… guardians of all that is good and moral and nice, and the black hats who are working at getting access to stuff that they shouldn’t have, that a locked door is a challenge and I want to get through that lock door just to see what’s there. And perhaps with nefarious intent. In cybersecurity, specifically, I see it as… where it’s always at the interface of where there are industries changing, for example, whereas more electronics and specific computers start to get on board like a Jeep Cherokee, that started to cause cars to be hackable, which was prior an unthinkable concept. And then, at DEFCON, the US Air Force had recently held a hack-a-sat, hacking satellite competition. And now, I’m not saying that those those issues are resolved. They’re still work in progress. But now we have the emergence of potentially accessible quantum computing that’s coming online — some evidence that this could work. And so that puts a threat to the ability for us with our usage of algorithms to encrypt data and storing it. And if I want to be mean, evil, I could grab any encrypted information I can find and sit on it for one year or one decade, whatever it takes for me to get access to a quantum computer and see what was discussed. Could you elaborate on this need for post-quantum security?
Matt Goldstein 51:33
Yeah, I mean, you already nailed the thesis, right? Which is fine. People talk about quantum as something in the future and something for us to develop, and they talk about how quantum will break all encryption. And that means we’ll need new encryption. And so people are building the computers, and they’re building the encryption for the computers simultaneously, and they think that’s all good. As long as those two things arrive within a few months of each other, everything’s fine. But to your point, the scariest part about quantum computer development is the fact that there is plenty of encrypted data sitting out there that people have saved or retained for a very long time that will suddenly be vulnerable. And certainly some of it is no longer relevant, but some of it is, right? Promised I wouldn’t talk about blockchain. So the one area where we spent a lot of time recently is in quantum key distribution. So this long term vision of the quantum internet, which is unbreakable point-to-point communication, where you know with absolute certainty whether a transaction, a packet, some element of communication has been intercepted or sniffed or spoofed is a beautiful vision. But there are challenges in distributing entanglement. And in so, you know, quantum computers operate on this concept of entanglement and entanglement has range concerns and range considerations. So if you agree with the fundamental premise, the beginning premise that we need to get kind of quantum resistant encryption set up before the quantum internet, two things are playing out. One is we need quantum safe for post-quantum algorithms. And the other thing is that we need to solve for this issue of quantum key distribution, making sure that the keys themselves aren’t intercepted and kept and sniffed. Yeah, so these are incredibly cool topics. I am far from an expert. I’m incredibly blessed to work with my colleague, Samir Kumar, who is our resident expert on the topic and is on the board of PsiQuantum. But it’s cool when we have a lot of fun riffing on the tangents between quantum and cyber.
JMill 54:11
That’s definitely a pretty extreme nerd level discussion.
Forrest Meyen 54:15
Yeah. We’re getting sci-fi pretty quick.
JMill 54:18
Yeah.
Forrest Meyen 54:20
I think we want to give you an opportunity to make whatever pitch you want for our audience. Whether it’s pitching M12 or just the importance of cybersecurity in your own life. But we just want to give you that last moment to have the last word.
Matt Goldstein 54:39
Sure. I’ll go back to what we talked about at the beginning, which is investing in optimism. And this is not me bragging saying I have the best job in the world. But I really do love my job. My job is to spend my days over the horizon and see what I can… see what small contribution I can make to bring those things closer to reality and closer to home. In your prep, you said, why is this important and who is it important to? It’s important to three people. It’s important to me personally, because it’s fun. And I feel good about what I do every day. Hopefully I’m doing well and doing good by the people who entrust me with their capital, and entrust me with their vision and their stories. And so hopefully I’m making money for my LPs and also helping these entrepreneurs achieve their dreams and giving them the capital and the resources they need to be successful. Look, I invest in companies that matter, I invest in companies that are doing cool things that aren’t cool for their own sake, but are fundamentally important to the future of our species, and the future of our society. I want to be investing in companies that are solving big problems, right? I’ll throw out one other random one, it has nothing to do with cybersecurity, but I led the series A in a company called Nautilus Labs in New York, which is voyage optimization, so speed and route optimization for the global shipping industry. The global shipping industry, most people know is the one of the largest polluters in the world that consume an enormous amount of a fuel that emits a lot of greenhouse gases. And it’s a particularly kind of tech-averse industry or legacy industry. Introducing software… very, very basic optimization and analytics, the kinds of things that every sophisticated software business does every single day inside their application performance monitoring solution… we can do that for ships. And we can tell captains and ship owners and operators, don’t go this way at six knots go that way at seven knots, you’ll still arrive at your destination… maybe I should flip the speed… you’ll still arrive at your destination on time, you’ll consume less fuel doing it. And by the way, when you get there, fill up at this place, not at that place. And I know the maintenance log says you don’t need to scrub the hall for another two months, but according to our data, you’re moving a little bit slower than we expected you to. And that’s probably due to the fact that you were hanging out in the Gulf of Mexico for three weeks when the water was two and a half degrees warmer than we normally expected it to be. And so we anticipate there’s some unnatural growth on the ship and that’s slowing things down. Oh, and by the way, when you go bring the ship in to get scrubbed, take it to this vendor, not that that vendor because according to our data, the ships perform this percentage better when they use that particular vendor to solve these problems. Incremental stuff can have an unbelievably enormous impact on businesses and on carbon emissions and on the world that we live in. And I think that’s cool. And that makes me happy. I’m Adam, managing director at M12. Stay tough.
Forrest Meyen 58:01
Thanks for tuning in to Tough Tech Today. We’ve just kicked off a brand new season, which means we’ll have another episode in only two weeks. In this episode, we’ll be talking with Virginia Burger. She’s the co-founder of New Equilibrium Biosciences. Please, if you enjoyed the show, spread the word. The best thing you could do on YouTube is leave a like, subscribe, and of course, leave a comment. We love interacting with our viewers. And if you’re on the podcast, leave us a five-star review and share with a friend. Thanks again and we’ll see you next time.